Legitima
Anti-counterfeiting product passports that bridge the private and public sector
Introduction
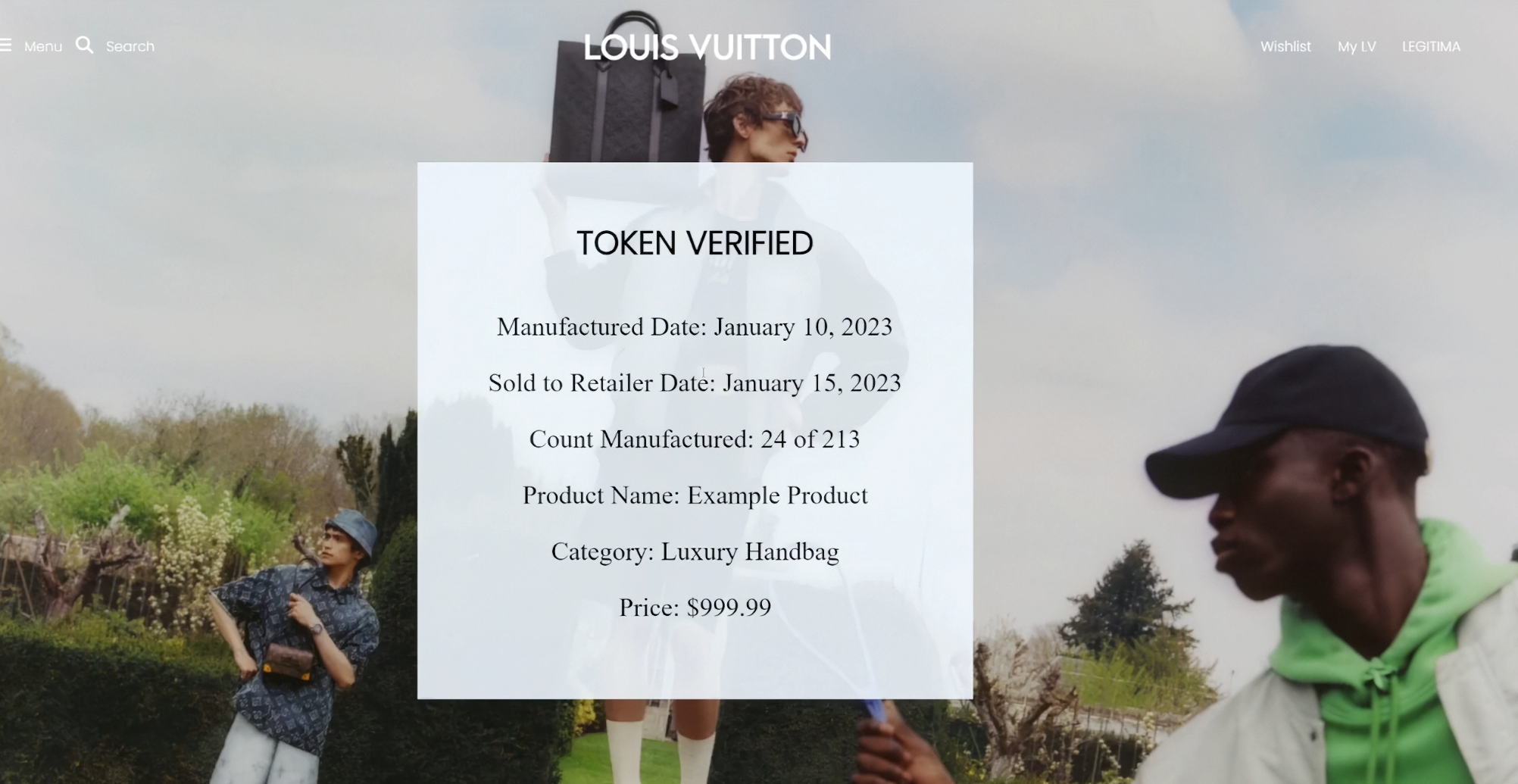
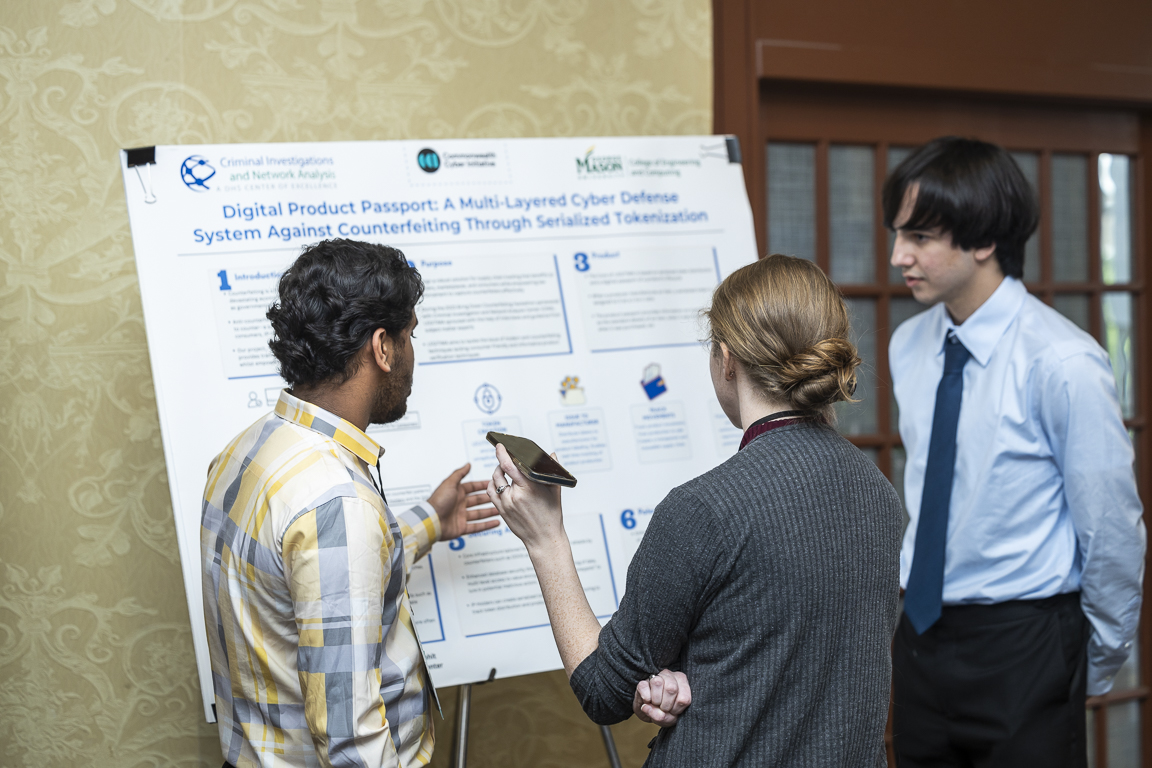
Legitima is an anti-counterfeiting solution that assigns every manufactured product a unique cryptographic token — a digital product passport. The system is designed to be dynamic and scalable: any business, regardless of budget, can integrate it and represent the token's access through whatever medium fits their workflow — RFID tags, barcodes, QR codes, or anything else. The product passport stores automatically updating information about the item's lifecycle, and customers or inspectors can cross-reference that data at any point to verify authenticity. The project won $10,000 in research funding and $1,000 for Best in Class at the 2023 Expedition Hacks hackathon, and later evolved into published research on accessibility in anti-counterfeiting solutions, which I solo presented at the IEEE 2024 TPS conference.
Software Developer (team of 2)
Purpose & Goal
Legitima was born out of a hackathon challenge to build a new anti-counterfeiting solution that bridges the private and public sector. A good friend and I teamed up, and the core idea was to create something that didn't just serve large corporations with big security budgets — it needed to scale down to small businesses too. The anti-counterfeiting space has a gap: most existing solutions are either expensive, proprietary, or hard to adopt. We wanted a system that any company could plug into their existing supply chain, and that gave end consumers a straightforward way to verify what they bought is real.
Technical Spotlight
The hardest problem was designing the mechanism for storing and updating product information inside each token in a way that was tamper-proof, timely, and useful. The workflow starts when a manufacturer requests tokens for a production run — one token per product, one-to-one. Each token holds static information like the date of manufacture, product details, and sale status. When a customer purchases the product and checks its passport, the stored information gets cross-referenced against what they're holding. If someone buys what's supposed to be an LV bag but the token says it's a brown Nike shoe, they know the token was replicated and the product is counterfeit. The same logic catches after-hours factory counterfeiting: if a token already shows the product as sold, a second item carrying that same token is a fake. The key challenge was deciding what information to store, when to update it, and how to ensure updates couldn't be tampered with. On the integration side, what prevents direct token copying is that companies host the passport verification through their own trusted systems — so even if someone replicates a token identifier, it won't return valid information from a legitimate source. I also designed the schema that defines what goes into the product passport, which determines what the system can and can't catch.
Lessons Learned
This was my first technical product that had a real audience critiquing and expanding on it. Presenting at the hackathon and later fielding questions from professionals in the anti-counterfeiting industry taught me how to adapt a product to stakeholder demands in real time — both technically and in how I communicated about it. After the hackathon, a good friend and I, under the guidance of a professional in the field, researched accessibility across different anti-counterfeiting solutions and their effectiveness for people with disabilities. That work became a published paper at the IEEE 2024 TPS conference, which I solo presented. The whole experience shifted how I think about building things: it's not just about whether the technology works, it's about who it works for and whether they can actually use it.